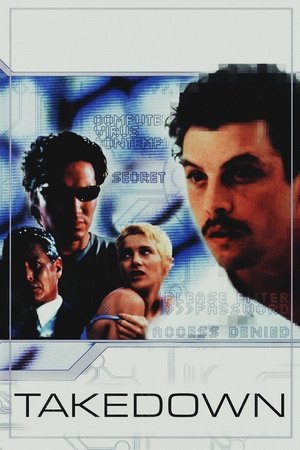
Takedown(2000)
The world has a right to know.
Kevin Mitnick is quite possibly the best hacker in the world. Hunting for more and more information, seeking more and more cyber-trophies every day, he constantly looks for bigger challenges. When he breaks into the computer of a security expert and an ex-hacker, he finds one - and much more than that...

Movie: Takedown
Video Trailer Takedown
Recommendations Movies
 5.9
5.9Dark Web: Cicada 3301(en)
Genius hacker Connor discovers Cicada 3301, an online treasure hunt that could be a recruiting tool for a secret society. Soon Conner, art-expert friend Avi, and secretive librarian Gwen are dashing from graffiti sites to ancient libraries to uncover real-world clues. But they must outrun aggressive NSA agents, also hot on the trail of Cicada, who want the glory for themselves.
 6.1
6.1The MacKintosh Man(en)
A member of British Intelligence assumes a fictitious criminal identity and allows himself to be caught, imprisoned, and freed in order to infiltrate a spy organization and expose a traitor; only, someone finds him out and exposes him to the gang...
 6.1
6.1Chief of Station(en)
After learning that the death of his wife was not an accident, a former CIA Station Chief is forced back into the espionage underworld, teaming up with an adversary to unravel a conspiracy that challenges everything he thought he knew.
 6.0
6.0Interceptor(en)
A U.S. Army Captain uses her years of tactical training to save humanity from sixteen nuclear missiles launched at the U.S. as a violent attack threatens her remote missile interceptor station.
 6.0
6.0Point Blank(en)
A nurse is forced to spring a wounded murder suspect from the hospital when the man’s brother kidnaps his pregnant wife and wants to make a trade.
 6.9
6.9Lights Out(en)
A drifting ex-soldier turns underground fighter with the help of a just-released ex-con, pitting him against corrupt cops and hired killers now gunning for him and all those he cares about.
 5.8
5.8Firewall(en)
State-of-the-art security system creator Jack Stanfield has cemented his reputation as a man who's thought of everything. But when a criminal finds a way into his personal life, everything Jack holds dear is suddenly at stake.
 6.0
6.0The Signal(en)
On a road trip, Nic and two friends are drawn to an isolated area by a computer genius. When everything suddenly goes dark, Nic regains consciousness – only to find himself in a waking nightmare.
 6.6
6.6Bad Sister(en)
As a top student at St. Adeline's Catholic Boarding School, Zoe senses that something is not quite right about the school's new nun-- a sense proven to be true when it is revealed the "good' nun is an imposter with a fatal attraction to Zoe's brother.
 6.6
6.6Live Free or Die Hard(en)
John McClane is back and badder than ever, and this time he calls on the services of a young hacker in his bid to stop a ring of Internet terrorists intent on taking control of America's computer infrastructure.
 5.9
5.9Suburbicon(en)
In the quiet family town of Suburbicon during the 1950s, the best and worst of humanity is hilariously reflected through the deeds of seemingly ordinary people. When a home invasion turns deadly, a picture-perfect family turns to blackmail, revenge and murder.
 6.6
6.6A Dry White Season(en)
During the 1976 Soweto uprising, a white school teacher's life and values are threatened when he asks questions about the death of a young black boy who died in police custody.
 5.9
5.9Hellion(en)
When motocross and heavy metal obsessed, 13-year-old Jacob's delinquent behavior forces CPS to place his little brother Wes with his aunt, Jacob and his emotionally absent father must finally take responsibility for their actions and each other in order to bring Wes home.
 6.2
6.2Locked(en)
When Eddie breaks into a luxury SUV, he steps into a deadly trap set by William, a self-proclaimed vigilante delivering his own brand of twisted justice. With no means of escape, Eddie must fight to survive in a ride where escape is an illusion, survival is a nightmare, and justice shifts into high gear.
 6.3
6.3Swordfish(en)
Rogue agent Gabriel Shear is determined to get his mitts on $9 billion stashed in a secret Drug Enforcement Administration account. He wants the cash to fight terrorism, but lacks the computer skills necessary to hack into the government mainframe. Enter Stanley Jobson, a n'er-do-well encryption expert who can log into anything.
 6.0
6.0Off the Grid(en)
After a morally-bankrupt company tries to weaponize a brilliant scientist's revolutionary technology, he goes off the grid to safeguard humanity. When the company sends a strike force to find him, they make their biggest mistake of all – they weaponize the man they are trying to catch.
 6.4
6.4The Commuter(en)
A businessman, on his daily commute home, gets unwittingly caught up in a criminal conspiracy that threatens not only his life but the lives of those around him.
 6.5
6.5The Good Neighbor(en)
A nightmarish evening unfolds for neighbors David and Robert when they accidentally hit a woman on her bike and flee the scene. While David is increasingly plagued by feelings of guilt, Robert shows no remorse and becomes overbearing and possessive.
 6.2
6.2The Girl in the Spider's Web(en)
After being enlisted to recover a dangerous computer program, hacker Lisbeth Salander and journalist Mikael Blomkvist find themselves caught in a web of spies, cybercriminals and corrupt government officials.
Similar Movies
 6.3
6.3Swordfish(en)
Rogue agent Gabriel Shear is determined to get his mitts on $9 billion stashed in a secret Drug Enforcement Administration account. He wants the cash to fight terrorism, but lacks the computer skills necessary to hack into the government mainframe. Enter Stanley Jobson, a n'er-do-well encryption expert who can log into anything.
 5.8
5.8Firewall(en)
State-of-the-art security system creator Jack Stanfield has cemented his reputation as a man who's thought of everything. But when a criminal finds a way into his personal life, everything Jack holds dear is suddenly at stake.
 5.1
5.1The Net 2.0(en)
The life of a young computer systems analyst is thrown into turmoil after arriving in Istanbul to start a new job. She soon finds her passport missing, her credit cards useless, her bank account empty and her identity stolen. As the story progresses we find people and events may not be what they seem.
 4.7
4.7Double Down(en)
An edgy action thriller set in Las Vegas during a terrorist attack. A genius computer loner takes control of the city and the attack as he fights with his fits of overwhelming depression and obsessions with love and death.
 5.5
5.5Cube 2: Hypercube(en)
Eight strangers awaken with no memory, in a puzzling cube-shaped room where the laws of physics do not always apply.
 0.0
0.0The Stables(en)
A vice detective must decide how far he will go in order to protect his informant.
 7.8
7.8Absolut(en)
Two guys against globalization want to plant a virus in the network of a finance corporation. On the day of the attack Alex has an accident and cannot remember anything. Visions and reality are thrown together in a confusing maze. Alex tries to escape from this muddle but what he discovers turns out to be rather frightening…
 7.1
7.1WarGames(en)
High school student David Lightman has a talent for hacking. But while trying to hack into a computer system to play unreleased video games, he unwittingly taps into the Department of Defense's war computer and initiates a confrontation of global proportions. Together with his friend and a wizardly computer genius, David must race against time to outwit his opponent and prevent a nuclear Armageddon.
 6.8
6.823(de)
The movie's plot is based on the true story of a group of young computer hackers from Hannover, Germany. In the late 1980s the orphaned Karl Koch invests his heritage in a flat and a home computer. At first he dials up to bulletin boards to discuss conspiracy theories inspired by his favorite novel, R.A. Wilson's "Illuminatus", but soon he and his friend David start breaking into government and military computers. Pepe, one of Karl's rather criminal acquaintances senses that there is money in computer cracking - he travels to east Berlin and tries to contact the KGB.
 6.6
6.6Live Free or Die Hard(en)
John McClane is back and badder than ever, and this time he calls on the services of a young hacker in his bid to stop a ring of Internet terrorists intent on taking control of America's computer infrastructure.
 7.6
7.6Who Am I(de)
Benjamin, a young German computer whiz, is invited to join a subversive hacker group that wants to be noticed on the world's stage.
 7.3
7.3Skyfall(en)
When Bond's latest assignment goes gravely wrong, agents around the world are exposed and MI6 headquarters is attacked. While M faces challenges to her authority and position from Gareth Mallory, the new Chairman of the Intelligence and Security Committee, it's up to Bond, aided only by field agent Eve, to locate the mastermind behind the attack.
Paranoia(en)
A girl, whose entire family was murdered by a serial killer, tries to isolate herself in New York City. Her fear escalates when the murderer starts stalking her on the internet. With his prison sentence about to end, the game of cat and mouse begins.
 8.3
8.3Flesh Dream(en)
After the death of their friend, two students discover a disturbing website that murders anyone that ventures too far into its domain.
 6.6
6.6Talhotblond(en)
This is the true story of a love triangle that takes place entirely online. Lies lead to murder in real life, as a teenage vixen (screen name 'talhotblond') lures men into her web. Revealing a shocking true crime story that shows the Internet's power to unleash our most dangerous fantasies.
 6.5
6.5Trust(en)
A suburban family is torn apart when fourteen-year-old Annie meets her first boyfriend online. After months of communicating via online chat and phone, Annie discovers her friend is not who he originally claimed to be. Shocked into disbelief, her parents are shattered by their daughter's actions and struggle to support her as she comes to terms with what has happened to her once innocent life.
 8.5
8.5Love Stalk(en)
Sharon is a fast-rising PR executive from Singapore, searching for love in Hong Kong, who may have found her dream guy, but as she chases after him online and in person, Sharon quickly finds out the dangers of stalking a secret crush.
 7.1
7.1The Girl Who Kicked the Hornet's Nest(sv)
After taking a bullet to the head, Salander is under close supervision in a hospital and is set to face trial for attempted murder on her eventual release. With the help of journalist Mikael Blomkvist and his researchers at Millennium magazine, Salander must prove her innocence. In doing this she plays against powerful enemies and her own past.
 4.8
4.8NetForce(en)
Set in the year 2005, a division of the FBI, called "NetForce" has been initiated to investigate Internet crime. A Bill Gates-type character finds a loophole in his new web browser which enables him to gain control of the Internet. Net-Force, headed by Kristofferson and Bakula's characters set out to stop him.