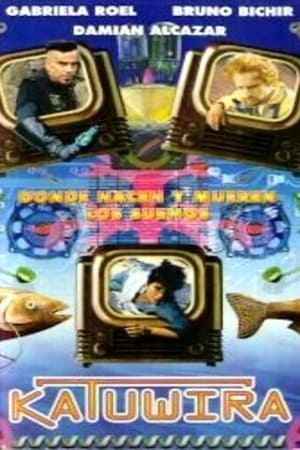
Katuwira, donde nacen y mueren los sueños(1996)
Sofia meets a stranger man who hacks the computer system where she works before she has an accident. After the accident, she is the only one that remember seeing this man, so she decides to search for him.
Movie: Katuwira, donde nacen y mueren los sueños
Top 8 Billed Cast
Solita
Vecina
Katuwira, donde nacen y mueren los sueños
HomePage
Overview
Sofia meets a stranger man who hacks the computer system where she works before she has an accident. After the accident, she is the only one that remember seeing this man, so she decides to search for him.
Release Date
1996-12-18
Average
5
Rating:
2.5 startsTagline
Genres
Languages:
Recommendations Movies
 6.0
6.0Antitrust(en)
A computer programmer's dream job at a hot Portland-based firm turns nightmarish when he discovers his boss has a secret and ruthless means of dispatching anti-trust problems.
 6.2
6.2The Girl in the Spider's Web(en)
After being enlisted to recover a dangerous computer program, hacker Lisbeth Salander and journalist Mikael Blomkvist find themselves caught in a web of spies, cybercriminals and corrupt government officials.
 7.9
7.9The Internet's Own Boy: The Story of Aaron Swartz(en)
Programming prodigy and information activist Aaron Swartz achieved groundbreaking work in social justice and political organizing. His passion for open access ensnared him in a legal nightmare that ended with the taking of his own life at the age of 26.
 6.0
6.0The Net(en)
Angela Bennett is a freelance computer systems analyst who tracks down software viruses. At night she hooks up to the internet and chats to others 'surfing the net'. While de-bugging a new high-tech game for a cyber friend, she comes across a top secret program and becomes the target of a mysterious organization who will stop at nothing to erase her identity and her existence, in order to protect the project.
 6.3
6.3The Chosen Ones(es)
Sofia, 14 years old, is in love with Ulises. Because of him, in spite of him, she is forced into a prostitution network in Mexico. To set her free, Ulises will have to find another girl to replace her. Adapted from Jorge Volpi’s novel, set in the world of juvenile prostitution.
 6.9
6.9Sneakers(en)
When shadowy U.S. intelligence agents blackmail a reformed computer hacker and his eccentric team of security experts into stealing a code-breaking 'black box' from a Soviet-funded genius, they uncover a bigger conspiracy. Now, he and his 'sneakers' must save themselves and the world economy by retrieving the box from their blackmailers.
 6.1
6.1The Night Before(en)
A popular beauty surprisingly asks a nerd to take her to the prom. He wakes up hours later in a sleazy alley. She's missing but he remembers nothing about it.
 6.5
6.52149: The Aftermath(en)
In an oppressive future, where everyone's only contact is their computer, one lonely young man is forced to venture forth in search of human contact.
 6.7
6.7Above the Shadows(en)
A young woman who has faded to the point of becoming invisible must find her way back with the help of the one man who can see her.
 7.0
7.0Call Me Crazy: A Five Film(en)
A psychotherapist helps a law student cope with schizophrenia in one of five interconnected tales dealing with mental illness.
 6.7
6.7Herself(en)
Struggling to provide her daughters with a safe, happy home, Sandra decides to build one - from scratch. Using all her ingenuity to make her ambitious dream a reality, Sandra draws together a community to lend a helping hand to build her house and ultimately recover her own sense of self.
 6.1
6.1The Zero Theorem(en)
A computer hacker's goal to discover the reason for human existence continually finds his work interrupted thanks to the Management; this time, they send a teenager and lusty love interest to distract him.
 7.0
7.0The Last Black Man in San Francisco(en)
Jimmie Fails dreams of reclaiming the Victorian home his grandfather built in the heart of San Francisco. Joined on his quest by his best friend Mont, Jimmie searches for belonging in a rapidly changing city that seems to have left them behind.
 6.5
6.5Fear the Invisible Man(en)
A young British widow shelters an old medical school colleague, a man who has somehow turned himself invisible. As his isolation grows and his sanity frays, he schemes to create a reign of wanton murder and terror across the city.
 8.0
8.0The Imitation Game(en)
Based on the real life story of legendary cryptanalyst Alan Turing, the film portrays the nail-biting race against time by Turing and his brilliant team of code-breakers at Britain's top-secret Government Code and Cypher School at Bletchley Park, during the darkest days of World War II.
 6.2
6.2Paycheck(en)
Michael Jennings is a genius who's hired – and paid handsomely – by high-tech firms to work on highly sensitive projects, after which his short-term memory is erased so he's incapable of breaching security. But at the end of a three-year job, he's told he isn't getting a paycheck and instead receives a mysterious envelope. In it are clues he must piece together to find out why he wasn't paid – and why he's now in hot water.
 6.3
6.3Underground: The Julian Assange Story(en)
In 1989, known as Mendax, Julian Assange and two friends formed a group called the International Subversives. Using early home computers and defining themselves as white hat hackers - those who look but don’t steal – they broke into some of the world’s most powerful and secretive organisations. In the eyes of the US Government, they were a major threat to national security.
 6.1
6.157 Seconds(en)
When a tech blogger lands an interview with a tech guru and stops an attack on him, he finds a mysterious ring that takes him back 57 seconds into the past.
 6.8
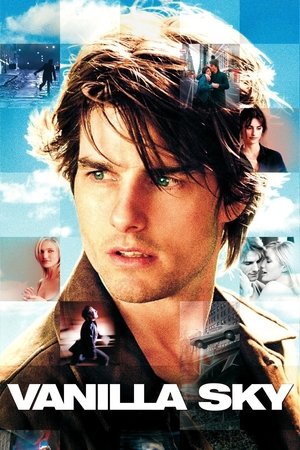
6.8Vanilla Sky(en)
David Aames has it all: wealth, good looks and gorgeous women on his arm. But just as he begins falling for the warmhearted Sofia, his face is horribly disfigured in a car accident. That's just the beginning of his troubles as the lines between illusion and reality, between life and death, are blurred.